EXECUTIVE SUMMARY
Wireless IoT devices are notoriously easy to hack. Often an attacker goes unnoticed as they assume the identity of an edge device and use it to connect with the network. Once in a network, the hacker may cause a great deal of damage or steal important information.
Endpoint Security is completing the development of a product that will give every fixed, wireless IoT device the ability to use multi-factor authentication. We hope to use it to eliminate a particularly elusive wireless cyber-attack vector, a man-in-the-middle attack. This type of attack stems from a perpetrator spoofing a wireless edge device after eavesdropping on the communications to learn its media access control (MAC) address, encryption key and password.
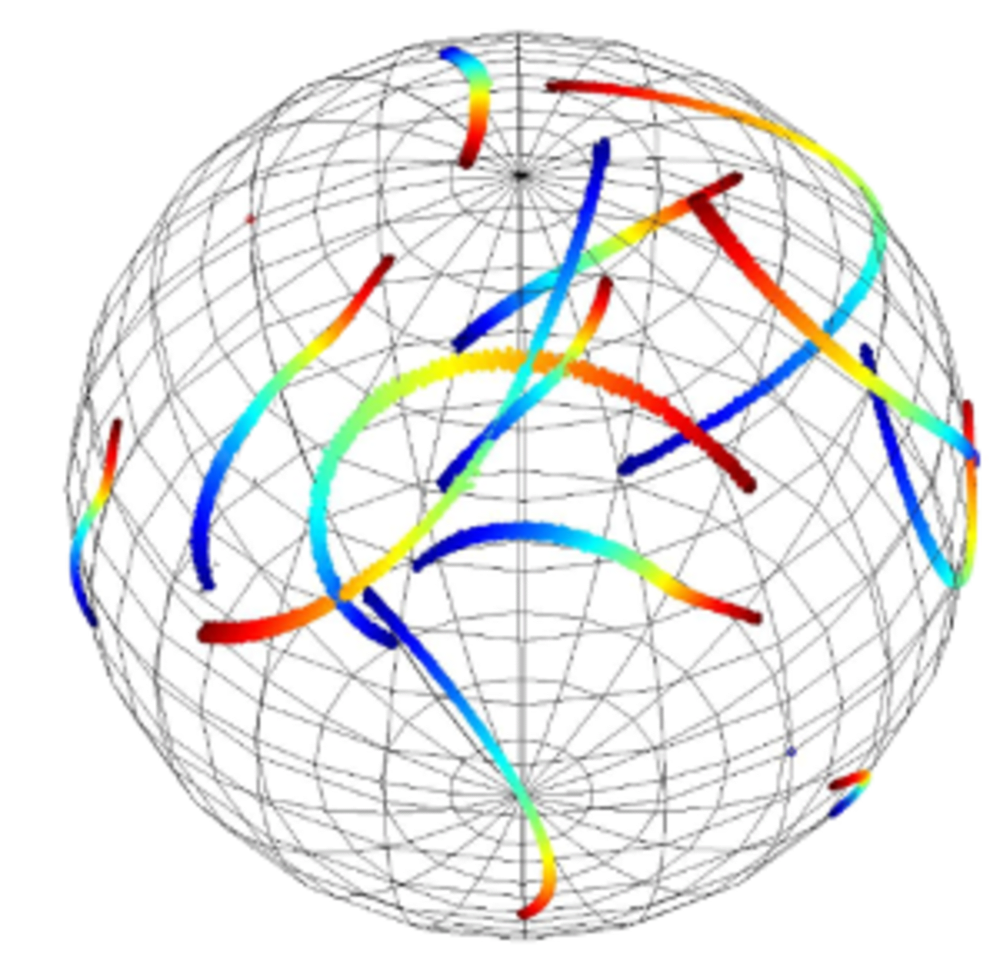
The solution will use a new physical-layer authentication process for fixed wireless devices. Endpoint Security has technology that sees a naturally occurring fingerprint in every radio frequency signal, independent of protocol or technology. It works as well with ZigBee, Bluetooth, radio, and WirelessHART as it does with WiFi. The fingerprint in the signal acts as multi-factor authentication, securing IoT with one of the best known methods of cybersecurity. This is all done without making any changes to the IoT device!
The fingerprint is seen from a characteristic of the signal called polarization mode dispersion. This characteristic has been tested extensively over the last two years and is found to be stable and robust. Every device that sends a wireless signal has this fingerprint inherently.
COMMERCIAL APPLICATIONS
Wireless Devices are becoming commonplace in many IoT applications; industry, commercial and consumer. We will begin with industrial Internet of things (IIoT) where
wireless devices collect data from a remote location, or a location within a plant with no available wiring, for process improvement. The move to Industry 4.0 leads the development of networks in this area. Often these devices are low power devices that have little capacity to do more than collect and send periodic data collected from a sensor. Security for such devices is often found lacking. Each one creates a potential entry point for man-in-the-middle attacks.
Artificial Intelligence techniques are common in wireless intrusion detection systems, including under its broad umbrella such tools as neural networks, machine-learning, pattern recognition and others. Such tools are difficult to use in an industry setting, however, since they learn a certain normalcy in communications traffic and send alerts based on changes. But, when a system fault occurs, or there is equipment failure, the communications traffic pattern becomes quite different. Yet, these are the conditions in which you most need the sensors to operate.
Momentum Partners marks this next generation security market at $4.4 billion growing at an astonishing 50% CAGR. Endpoint will license our technology manufacturers of access points, like routers and gateways. They can incorporate it into chipsets already in their equipment and instantly implement multi-factor authentication for IoT devices. Consumer devices could follow. Endpoint wants to @EndHackers.
Video
-
Awards
-
 2020 Electronics/Sensors/IoT Honorable Mention
2020 Electronics/Sensors/IoT Honorable Mention -
 2020 Top 100 Entries
2020 Top 100 Entries
Like this entry?
-
About the Entrant
- Name:Page Heller
- Type of entry:individual
- Software used for this entry:Python interpreter and C++ compiler
- Patent status:patented