Cloud storage is gaining popularity. In enterprise settings, we see the rise in demand for data outsourcing, which assists in the strategic management of corporate data. It is also used as a core technology behind many online services for personal applications. Nowadays, it is easy to apply for free accounts for email, photo album, and file sharing and/or remote access, with storage size more than 25 GB (or a few dollars for more than 1 TB ). Together with the current wireless technology, users can access almost all of their files and emails by a mobile phone in any corner of the world. Its flexible and cost optimizing characteristic motivates the end user as well as enterprises to store the data on cloud.The insider attack is one of security concern which needs to be focused. Cloud Service provider need to make sure whether audits are held for users who have physical access to the server. As cloud service provider stores the data of different users on same server it is possible that user's private data is leaked to others. The public auditing system of data storage security in cloud computing provides a privacy-preserving auditing protocol .
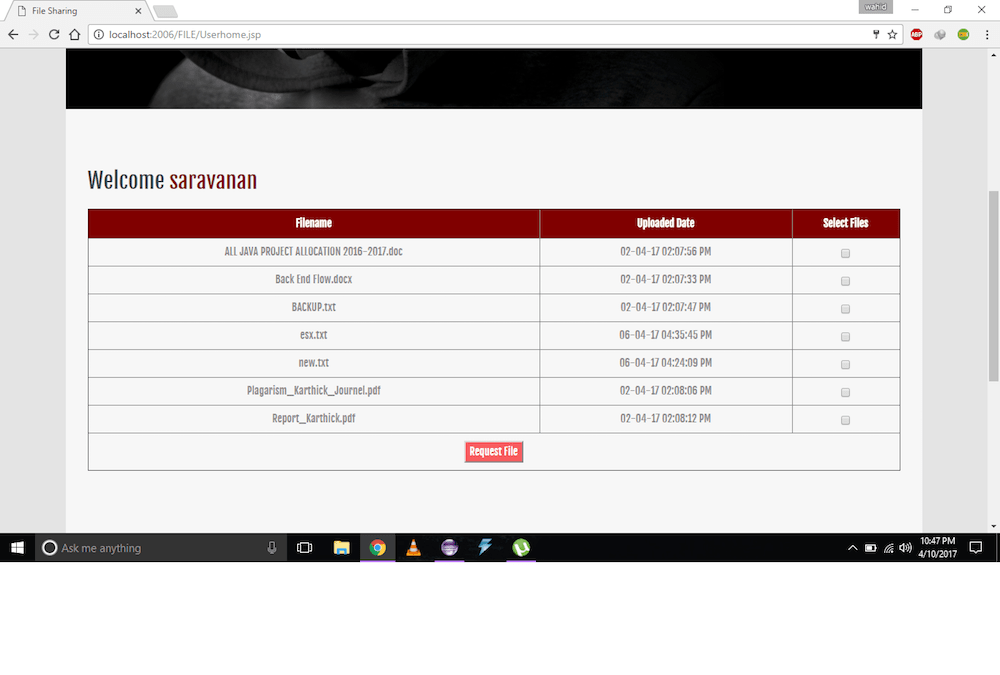
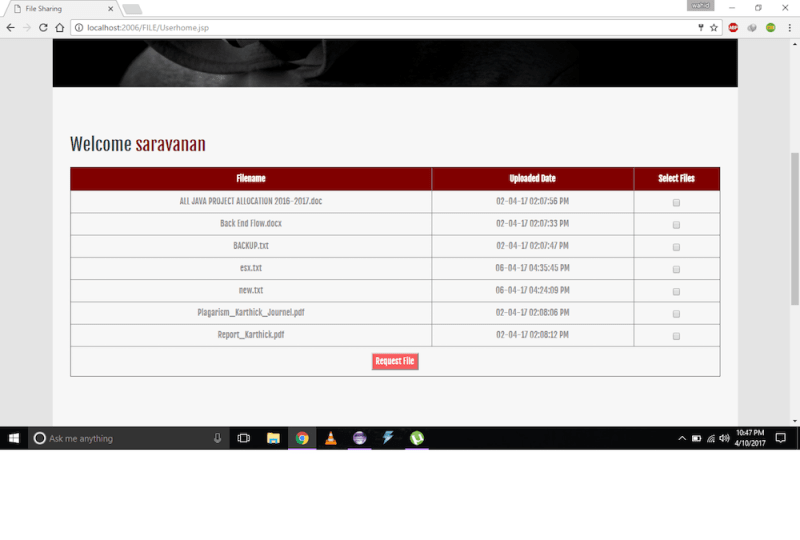
A new way for public-key encryption is used called as key aggregate cryptosystem (KAC). The encryption is done through an identifier of Cipher text known as class, with public key. The classes are formed by classifying the cipher text. The key owner has the master secret key which-is helpful for extracting secret key. So in above scenario Alice can send a aggregate key to bob through a email and the encrypted data is downloaded from drop box through the aggregate key. Cloud computing is visualized as architecture for succeeding generation. It has many facilities though have a risk of attacker who can access the data or leak the user's identity. While setting a cloud users and service providers authentication is necessary. The issue arises whether the cloud service provider or user is not compromised. will leak if any one of them in compromised. The cloud should be simple, preserving the privacy and also maintaining user's identity .The flexible use of cloud storage for user is a need as it is seams accessing data locally though that is present at remote side. It is important to inspect the data set on the cloud. So it's necessary to allow a public audit for integrity of outsourced data through third party auditor (TPA). TPA is also beneficial for cloud service provider. It checks the correctness of the outsourced data. TPA should be able to do public audibility, storage correctness, privacy preserving, Batch auditing with minimum communication and computation overhead. There are many cloud users who wants to upload their data without providing much personal details to other users. The anonymity of the user is to be preserved so that not to reveal the identity of data owner. Provable data possession (PDP) uses similar demonstrating marks to reduce computation on server, and network traffic. PDA ensures the data is present on the cloud.
Like this entry?
-
About the Entrant
- Name:Vijay Kumar
- Type of entry:teamTeam members:Vijay Kumar Wahid Khan Sreedev Nair
- Software used for this entry:Eclipse,TomCat,MySQL
- Patent status:none