2020
Entries
We are an innovative startup with a social vocation the PREINVEL, that has designed and developed the sole FLUIDODYNAMIC FILTERING technology in the world able to clean the pulluted industrial emissions and remove the smallest dust and pollutants, extremely dangerous for human's healt and so dangerous for the environmental,
The present invention relates to design and fabrication of new supports; which are in fact polymer-metal composite supports for finger, foot and spine. They are made of a soft polymer with inserted sheets of aluminum, steel or carbon-fiber. The optimal models are strong,

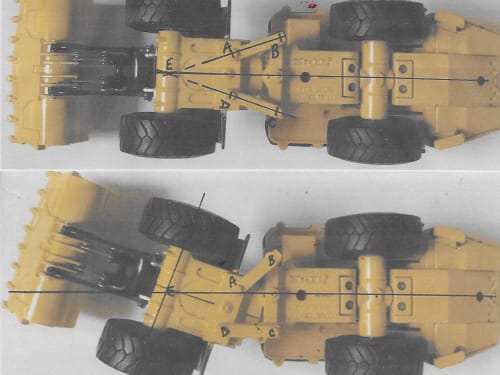
Frame steered construction vehicles, Articulated Dump Trucks (ADT), Wheeled Loaders, are known to be unstable at elevated speeds presenting safety/productivity concerns. Literature on this issue deals only with measures such as control systems to reduce instability.
The cause of instability, rear wheel steer, is not addressed.
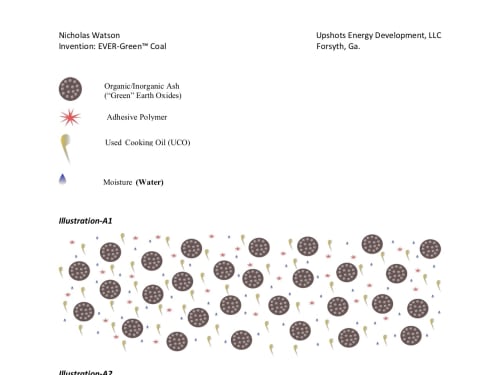
According to the World Coal Association (https://www.worldcoal.org/), the energy and cost benefits associated with coal combustion plays a vital role in the robustness of the electric-power generation, steel, and cement industries. Coal combustion accounts for 37% of global electricity generation.
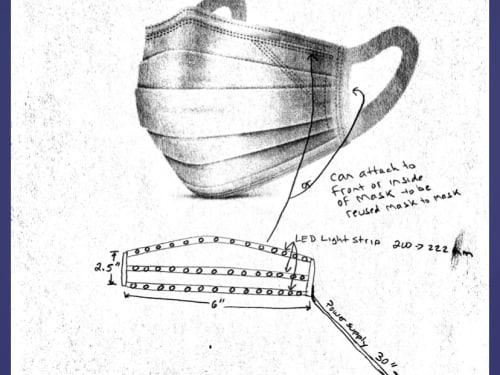
- Product was inspired from preemie son (few weeks old) who overcome the pneumonia virus and realized that there is a need to invent germ free products.
- A solution focused on the kitchenware industry.
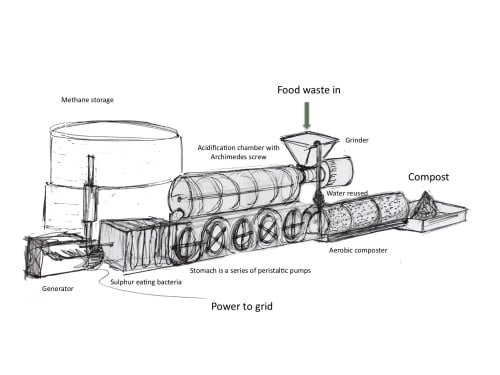
This product is a community sized unit that converts food waste to energy and compost. Each American produces 231lbs of food waste a year. Rather than this being a problem it can be a valuable commodity.
Food waste is a noxious material if dumped on landfill.
The proposed super-resolution multiplexed line scan microscopy system realizes photon reassignment (PRA) microscopy technique for imaging fluorophore-labeled specimens. Unlike existing PRA techniques with a restricted two-fold resolution enhancement, the present system surpasses diffraction Abbe limit by a factor m=〖(σ_D/σ_E)〗^2+1>

 EXECUTIVE SUMMARY
EXECUTIVE SUMMARYWireless IoT devices are notoriously easy to hack. Often an attacker goes unnoticed as they assume the identity of an edge device and use it to connect with the network. Once in a network, the hacker may cause a great deal of damage or steal important information.
Page 39 of 57