2017
Electronics/Sensors/IoT
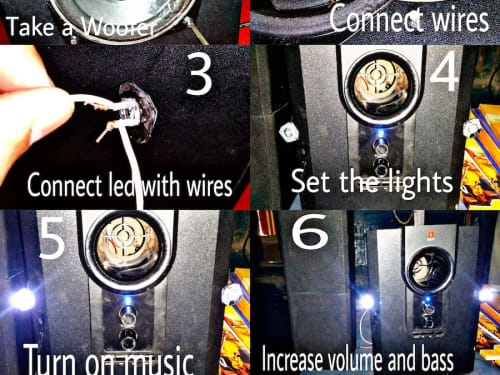
I have connected LED lights in a way that they all glow at the same time with the pulse of music.
I had connected both lights directly to a subwoofer so the current which is going in the wire of woofer is divided and the same current goes to the lights also. The more we increase the volume and bass,
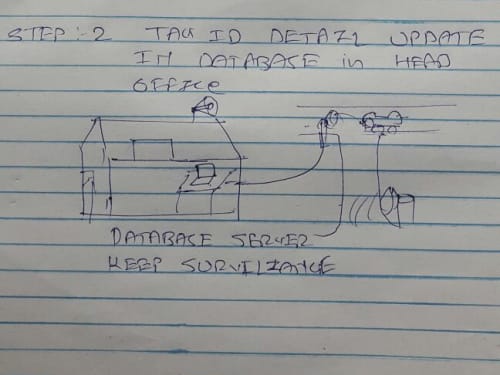
RFID is a tag that can be used to track or to check availability of anything. Using RFID tag we can attach with vehicle (2 wheeler, 4 wheeler, etc.) as turning point of every street or any hub (road junction). Put passive RFID sensor to passed vehicle list with unique tag id.
I am in this contest to buy materials for the FREE classes I teach on beginner robotics/animatronics.
The RoboGuts circuit board is designed to host most of the MCU chips or modules on the market today in a footprint the same size as an Arduino UNO board.
Design statement:
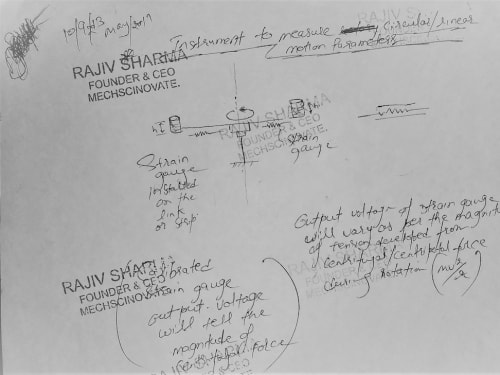
The instrument has following parts,
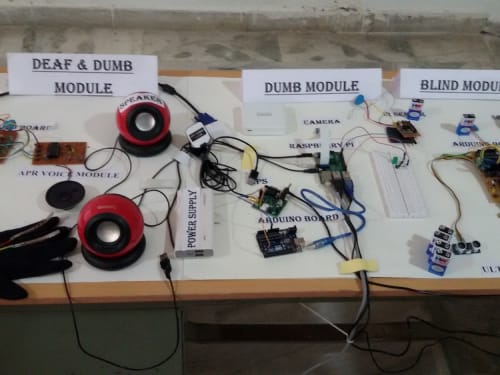
The project is an embedded system which works on Raspberry Pi using a sensor. The sensor detects the hurdles and sends the data to the Raspberry Pi. Raspberry Pi examine the data and send details to the user in the form of Speech. The whole route is narrated to the user.
I hold the IP portfolio surrounding the space of GPS/LBS enabled keys, also trademarked "SafeKey".
SafeKey is best understood as "OnStar on your keys." SafeKey places a GPS personal locator panic button on the common key, at an enterprise/supplier level - it is instant safety at everyone's fingertips.
SAFER (“Safe And Feasible Exponential Risk”) Diamond® is a novel risk assessment and management tool, with a user-friendly graphical presentation format of data and results.
While incorporating the best features of the familiar Risk Matrix to obtain quantitative risk (R) as product of probability (P) and severity (S) of loss, and ALARP (“As Low As Reasonably Practicable”
Almost everyone has milk as the first drink in their life. In infancy it is the mother's milk. In childhood, youth and adulthood it's a cow's or goat's milk. It is worth noting that the older a person becomes the more the distance increases between the source of milk and its consumer.
This new gun fired or rocket launched scout surveilance bullet / projectile photographs miles of land in seconds while radio transmiting its colored imagery to a remote radio receiver, computer, amd display. This scout surveillance projectile is comprised of a casing, high speed camera image sensors (with lenses), battery, radio transmitter, time clock, GPS receiver, inertial switch, inertial accelerometer,
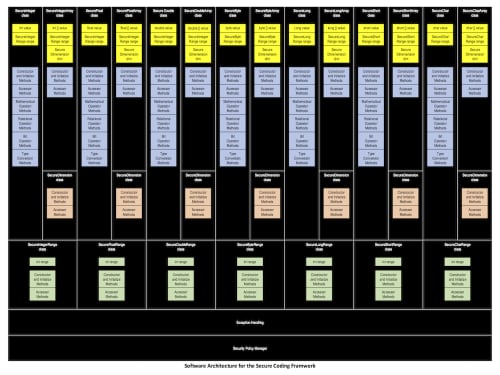
Secure Coding Framework (SCF)
Innovation
The SCF addresses the problem of application cybersecurity head-on with a powerful new development platform for building secure code from the ground up. It is the equivalent of a new secure programming language, but better. Mainstream programming languages in use today such as C++, C# and Java were designed in the 70’s and 80’s.
Page 9 of 12